It started with a straightforward architecture decision: keep identity on-prem under your control while still using Microsoft 365 in the cloud.
That’s the challenge Qudora Technologies GmbH brought to SerNet. QUDORA is a leading full-stack quantum computing company based in Germany. The company’s proprietary Near-Field Quantum Control (NFQC®) technology brings together ultra precise qubit control with very long coherence times significantly improving the performance per qubit. QUDORA’s QC systems are designed for seamless integration with existing industrial infrastructure, including on-premise deployments for HPC centers. With operations in Braunschweig and Hamburg, QUDORA is making quantum computing accessible to a broader range of applications and industries.
Qudora approached SerNet because the Göttingen-based open-source specialist combines upstream Samba engineering with hands-on integration expertise across Samba and Microsoft environments.
Project snapshot
- On-prem authoritative directory: Samba Active Directory Domain Controller
- Cloud services: Microsoft 365 (Exchange Online, SharePoint, Teams)
- Sync engine: Microsoft Entra Connect (one-way: on-prem → cloud)
- Key requirement: Exchange-relevant attributes available and correct in Samba AD
- Goal: Production-ready hybrid setup
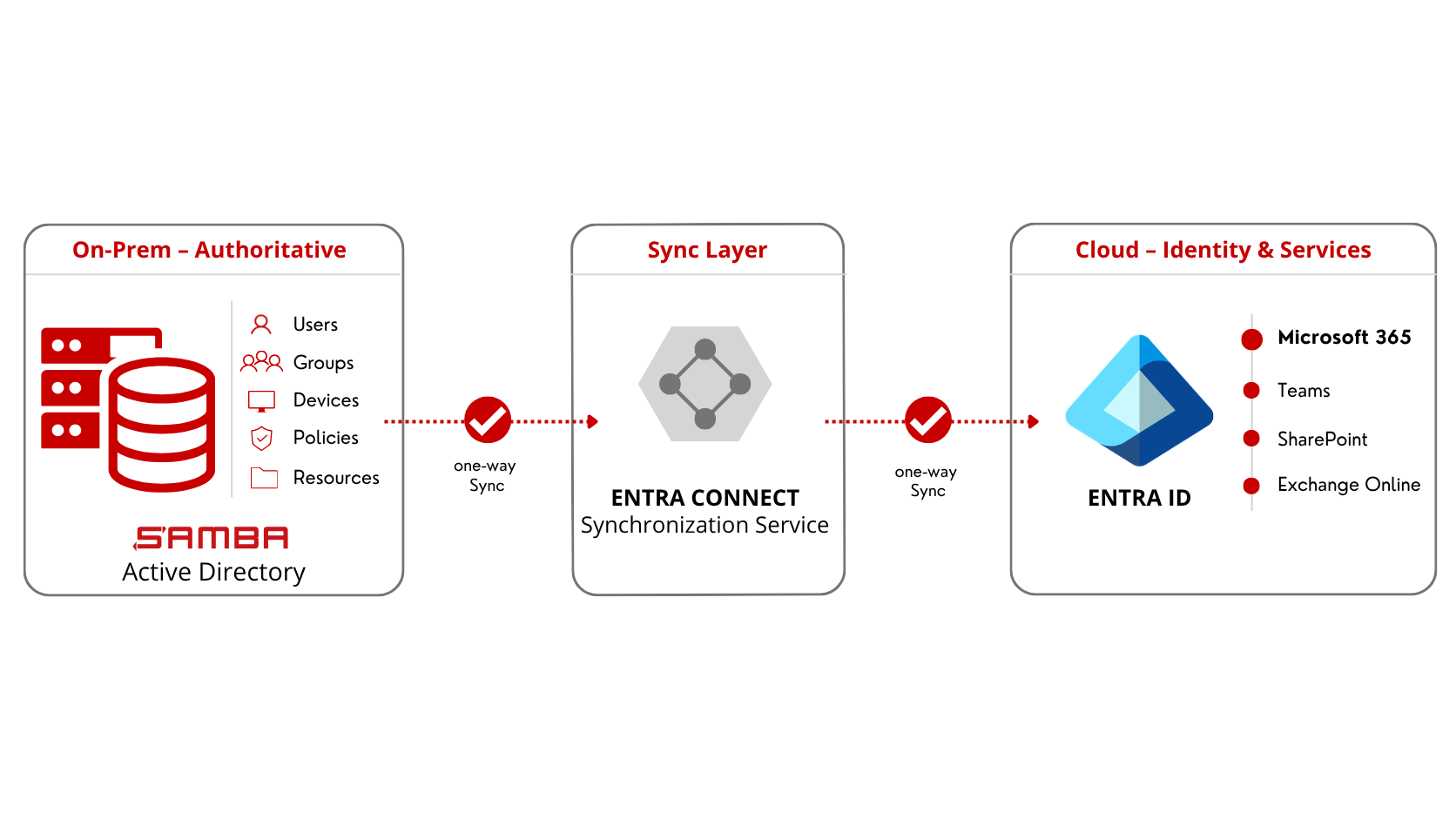
Architecture: On-Prem Stays Authoritative
The core question was simple: Can a Samba AD domain synchronize cleanly to Microsoft Entra ID using Entra Connect – including the Exchange-relevant attributes.
In many real-world environments, Exchange requirements have historically pushed teams toward “just use Windows for AD,” because Exchange Online (and hybrid patterns around it) expect specific object classes and attributes.
Qudora wanted a different design that takes digitial sovereignty requirements serious: Samba AD stays the source of authority, Microsoft 365 consumes synchronized identities, and admins manage users in one place.
The Engineering Core: Bringing Exchange Attributes to Samba AD
The challenge wasn’t “getting sync to run.” The challenge was meeting the schema and attribute expectations that come with Exchange.
Exchange Online commonly relies on attributes and structures such as:
- proxyAddresses
- mail
- targetAddress
- multiple msExch* attributes
- Exchange organization objects / related classes
To meet those requirements with Samba as the only AD DC, the project required:
- Extending the LDAP schema in Samba AD for Exchange-relevant object classes and attributes
- Targeted Samba code changes so these objects were handled correctly
- Protocol-level troubleshooting (network traces + deep debug logs) to confirm what Entra Connect was actually requesting and how Samba responded
This is where SerNet’s team setup mattered in a very concrete way:
- Björn Jacke (Integrator in SerNets Samba Team) led the AD-side implementation and guided the Samba AD/DC requirements.
- Stefan Metzmacher (Samba core development) traced the behavior down to the relevant code paths and implemented the fixes.
- Carl Massiang (Integrator in SerNets Secure Infrastructures Team) implemented the Entra Connect configuration and handled the Microsoft 365 / Exchange Online integration work.
The resulting changes were merged upstream, so the broader Samba community benefits as well.
A key point from the field: from Entra ID’s perspective, this behaved like a standard Active Directory environment. Entra “didn’t care” that the DC was Samba.
The solution in production
Once in place, the operational flow was clean and repeatable:
- Create/manage users in the on-prem Samba AD (the authoritative directory).
- Set Exchange-relevant attributes in Samba AD.
- Entra Connect synchronizes objects one way (on-prem → Entra ID).
- Microsoft 365 provisions the Exchange Online mailbox automatically based on the synchronized identity and attributes.
No on-prem Exchange server was required for this setup. No extra Windows domain was added. No double maintenance of identities. Only one Windows Member Server for the Entra Connect Sync Service is needed.
What changed for Qudora
This implementation delivered a hybrid identity design that was:
- single-source-of-truth (on-prem Samba AD)
- cloud-ready for Microsoft 365 services
- schema-correct for Exchange Online expectations
- stable and reproducible in production
In a follow-on project with another company, the same approach was applied to a hybrid scenario involving an on-prem Exchange server, where domain controllers must evaluate certain policies correctly for Exchange objects to provision as expected. That scenario was achievable as well, building on the extended schema foundation.
Planning something similar?
If you run Samba AD and want to connect Microsoft 365 or you need to harden an existing hybrid setup, reach out to SerNet. We’ll review your directory model and schema, validate Exchange attribute requirements, design the Entra Connect architecture, and implement it end-to-end – including upstream-grade troubleshooting when the issue is deeper than configuration.
Note on digital sovereignty: Depending on your requirements, SerNet also designs and implements sovereign alternatives without Microsoft cloud services – on-prem or with European providers – especially where data residency, regulatory constraints, or risk considerations (including topics like the U.S. CLOUD Act) are part of the decision.
SerNet can do this, just reach out.